Penetration Testing for Universities: Securing Higher Education Environments
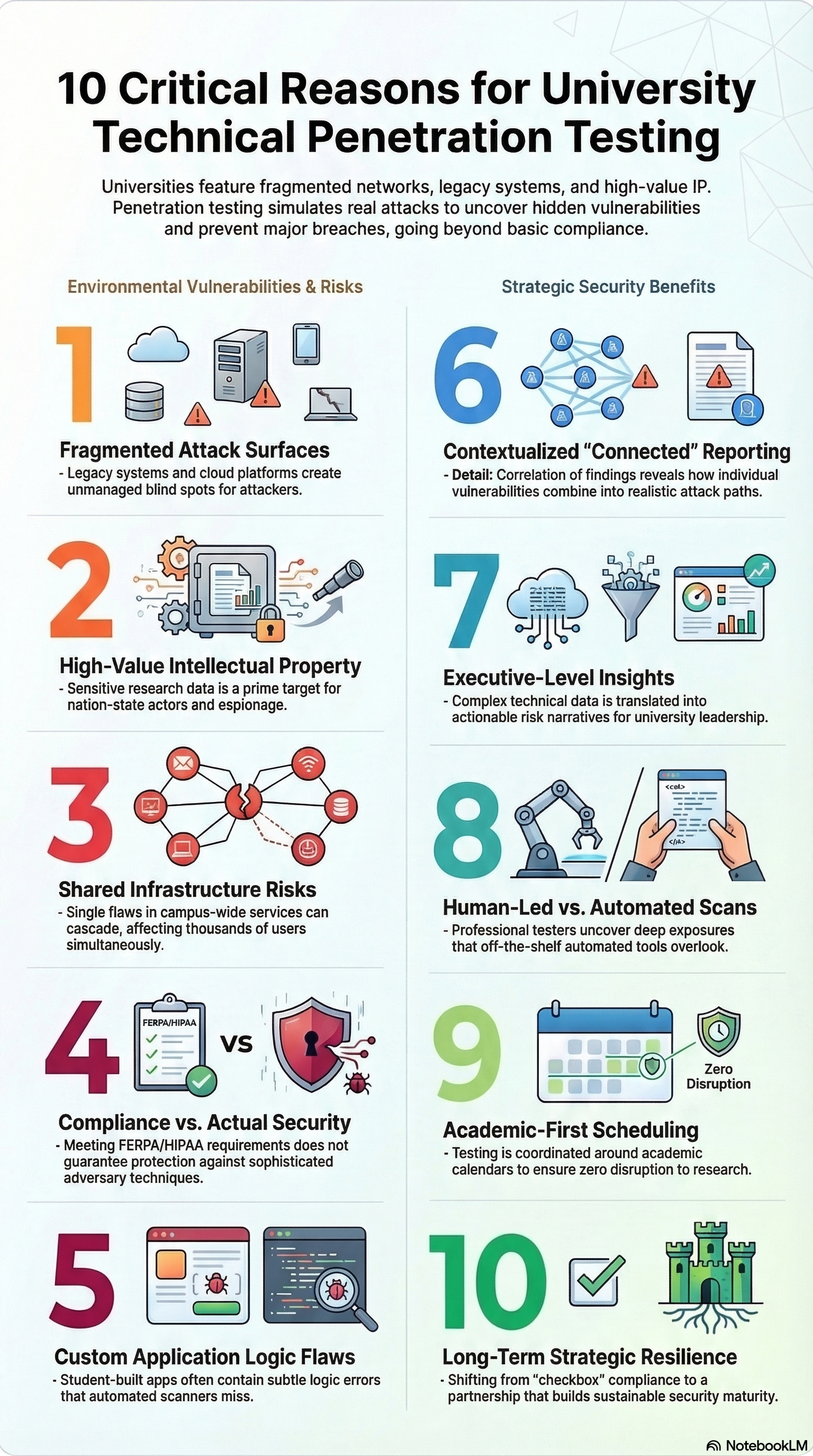
10 Critical Reasons Why Universities Need Technical Penetration Testing
Universities are complex digital ecosystems, handling everything from student records and faculty research to cloud services and legacy systems. This makes them prime targets for cyberattacks, data breaches, and intellectual property theft. Technical penetration testing is the most effective way to uncover hidden vulnerabilities before attackers do. In this article, we break down the top reasons why universities need penetration testing, showing how proactive security protects students, faculty, and the valuable data that powers academic innovation and provide a real-world case study from a university we served.
1. Universities Have Uniquely Large and Fragmented Attack Surfaces
Operating within a complex ecosystem, universities often rely on decades-old legacy systems, modern cloud platforms, research networks, student portals, and third-party vendor integrations. This creates thousands of interconnected assets, many of which are unmanaged, undocumented, or difficult to track. This fragmentation also creates blind spots that attackers can exploit, allowing them to move laterally across networks, access sensitive research, or compromise personal data.
Exploit Strike specializes in mapping and testing these real-world attack surfaces, uncovering hidden vulnerabilities that go far beyond what traditional inventory lists or automated scans can identify. By simulating sophisticated adversary behavior, we provide universities with a clear, actionable understanding of where their most critical risks lie and how to mitigate them.
2. Sensitive Research and Intellectual Property Are High-Value Targets
Universities are treasure troves of sensitive and high-value information, including grant-funded data, unpublished research, proprietary intellectual property, and work that may attract attention from nation-state actors. This makes them uniquely appealing targets for cybercriminals, corporate espionage, and sophisticated threat actors.
At Exploit Strike, we approach penetesting from the perspective of a motivated adversary, not just a checklist auditor. We simulate advanced attack techniques, carefully chaining together vulnerabilities across multiple systems and applications to uncover hidden paths that could lead to sensitive research assets. We reveal realistic attack scenarios, showing not only where a breach could occur, but also the potential impact on research integrity, intellectual property, and the university’s reputation. This proactive approach helps institutions close gaps before attackers have a chance to exploit them.
3. Shared Infrastructure Amplifies Risk
Higher education institutions rely heavily on shared infrastructure; multi-tenant hosting environments, centralized identity providers, and campus-wide services such as email, learning management systems, and research collaboration platforms. While these centralized systems improve efficiency, they also amplify risk: a single misconfiguration, weak credential, or unpatched vulnerability can potentially affect thousands of users and multiple departments simultaneously.
Our internal penetration testing goes beyond identifying isolated vulnerabilities. We focus on blast radius, mapping how a single flaw could spread across the campus, privilege escalation, and lateral movement opportunities that attackers could exploit to gain deeper access. This approach provides universities with a clear understanding of how vulnerabilities can cascade, enabling security teams to prioritize remediation efforts where they will have the greatest impact in reducing campus-wide risk.
4. Compliance Alone Is Not Security
Meeting FERPA, HIPAA, GLBA, or grant-specific cybersecurity requirements is essential for legal and regulatory purposes, but it does not guarantee your university’s environment is secure. Compliance frameworks often focus on policies, documentation, and basic technical controls, leaving gaps that attackers can exploit.
Our team goes beyond checklist testing, simulating real-world adversaries to uncover vulnerabilities that matter most. By focusing on attack paths, exploitability, and the actual techniques cybercriminals use, we help universities identify hidden weaknesses that compliance audits might miss. This ensures that security measures are not just about passing inspections, but about truly protecting sensitive student records, research data, and critical intellectual property from real threats.
5. Student-Built and Legacy Applications Introduce Unique Vulnerabilities
Universities leverage a mix of custom-built applications developed over years by rotating teams of students, faculty, and IT staff. While these apps are critical for learning, research, and administration, they frequently contain subtle logic flaws, insecure coding patterns, or overlooked configuration issues. Standard vulnerability scanners may flag known CVEs, but they often miss deeper problems in how the application actually functions, such as authentication bypasses, improper access controls, or business logic errors.
Exploit Strike specializes in reviewing and testing real application logic, simulating how an attacker would interact with the system in practice. By examining how all components work together rather than just looking for known vulnerabilities, we uncover hidden risks that could allow unauthorized access to sensitive data, disrupt services, or expose intellectual property. This ensures universities gain a practical understanding of their application security posture and actionable guidance for remediation.
6. We Connect the Dots Across Findings
Many security vendors provide long lists of disconnected vulnerabilities, leaving IT teams with raw data but little clarity on which issues pose the greatest risk. This can make it difficult to prioritize remediation effectively, wasting time and resources while critical weaknesses remain unaddressed.
Our team takes a different approach with an all-hands-on-deck pentesting model led by an experienced lead engineer. Every finding is correlated and contextualized, connecting the dots across systems, applications, and user workflows to highlight how individual vulnerabilities could be exploited in real-world attack scenarios. The result is a prioritized, actionable report that empowers decision-makers to focus on the most critical risks first, allocate resources efficiently, and strengthen the university’s security posture in a meaningful, measurable way.
7. Executive-Level Reporting for Leadership and Boards
Universities operate in an environment where both technical expertise and clear communication are critical. While deep technical assessments uncover vulnerabilities, they can be difficult for leadership teams to interpret and act on without context.
Exploit Strike bridges this gap by delivering reports that translate complex attack paths into clear, actionable risk narratives. We explain not just what vulnerabilities exist, but how they could be exploited, what the potential impact would be, and which fixes will have the greatest effect. Each technical report contains an executive summary designed for CISOs, CIOs, legal teams, and boards, providing the strategic insight needed to make informed decisions about cybersecurity investments, prioritizing remediation, and reducing risk across the entire institution. This ensures that technical findings don’t just sit in a report, they become a roadmap for meaningful, campus-wide security improvements.
8. Real Adversary Perspective, Not Automated Output
Many traditional security assessments heavily utilize automated scanners and off-the-shelf tools, which can overlook subtle vulnerabilities or complex attack chains.
At Exploit Strike, we take a real-world adversary approach, combining custom-built tooling with OSINT-driven reconnaissance to uncover exposures that automated scanners often miss. Our team digs deep into the code, infrastructure, and operational behavior of university systems, analyzing how an attacker might move through networks, exploit applications, and escalate privileges. By simulating these realistic attack scenarios, we identify hidden weaknesses that could lead to data breaches, intellectual property theft, or disruption of critical services. This approach ensures universities gain a comprehensive understanding of their security posture, including the risks that matter most in practice, not just the ones that show up on a generic scan.
9. Minimal Disruption While Maximizing Insight
Academic environments have unique operational demands: ongoing research experiments, live student services, online classes, and critical administrative systems all require continuous uptime. A poorly timed penetest could interrupt these essential operations, causing lost productivity, research delays, or service outages.
Our executive team carefully designs testing around academic calendars, research schedules, and operational sensitivities, ensuring that assessments are thorough yet non-disruptive. We coordinate with university IT staff to schedule tests, simulate realistic attack scenarios, and probe systems without impacting day-to-day activities. The result is deep, meaningful security insights that reveal true vulnerabilities and risk paths, while allowing students, faculty, and staff to continue their work uninterrupted. This balance of rigor and operational awareness ensures universities can strengthen their security posture without compromising their mission.
10. A Long-Term Security Partner, Not a One-Off Vendor
Cybersecurity isn’t a one-time project, it’s an ongoing process of improvement and adaptation. Many institutions treat penetesting as an annual “checkbox exercise,” addressing only the immediate findings without building long-term security maturity.
Exploit Strike takes a strategic, partnership-driven approach, working closely with universities to not only identify vulnerabilities but also support remediation, retesting, and continuous risk reduction. We help IT and security teams prioritize fixes, implement best practices, and track progress over time, ensuring that improvements are sustainable and aligned with evolving threats. By focusing on long-term resilience rather than isolated tests, we enable universities to strengthen their overall security posture, protect sensitive data, and confidently demonstrate proactive risk management to stakeholders, researchers, and students alike.
Case Study on Penetration Testing for Universities: When Student Code Becomes Institutional Risk
Universities face a risk profile most enterprises never deal with. They run critical institutional systems alongside student and faculty-built applications, often on the same infrastructure. As a result, some of the most exposed systems in higher education are also the least scrutinized during network security audits or penetration testing. These systems are internet-accessible and lightly governed (if at all). When they are hosted incorrectly, a single vulnerable student application can compromise an entire university web presence. However, a good pentest can bring visibility to this.
This case study explains:
Why student and faculty web environments must be in scope for university penetration testing
How shared hosting turns low-risk code into high-impact failures
A real case study where a student web app compromised the root domain
What universities should change architecturally
Why timing penetration tests or other security audits around the academic calendar matters
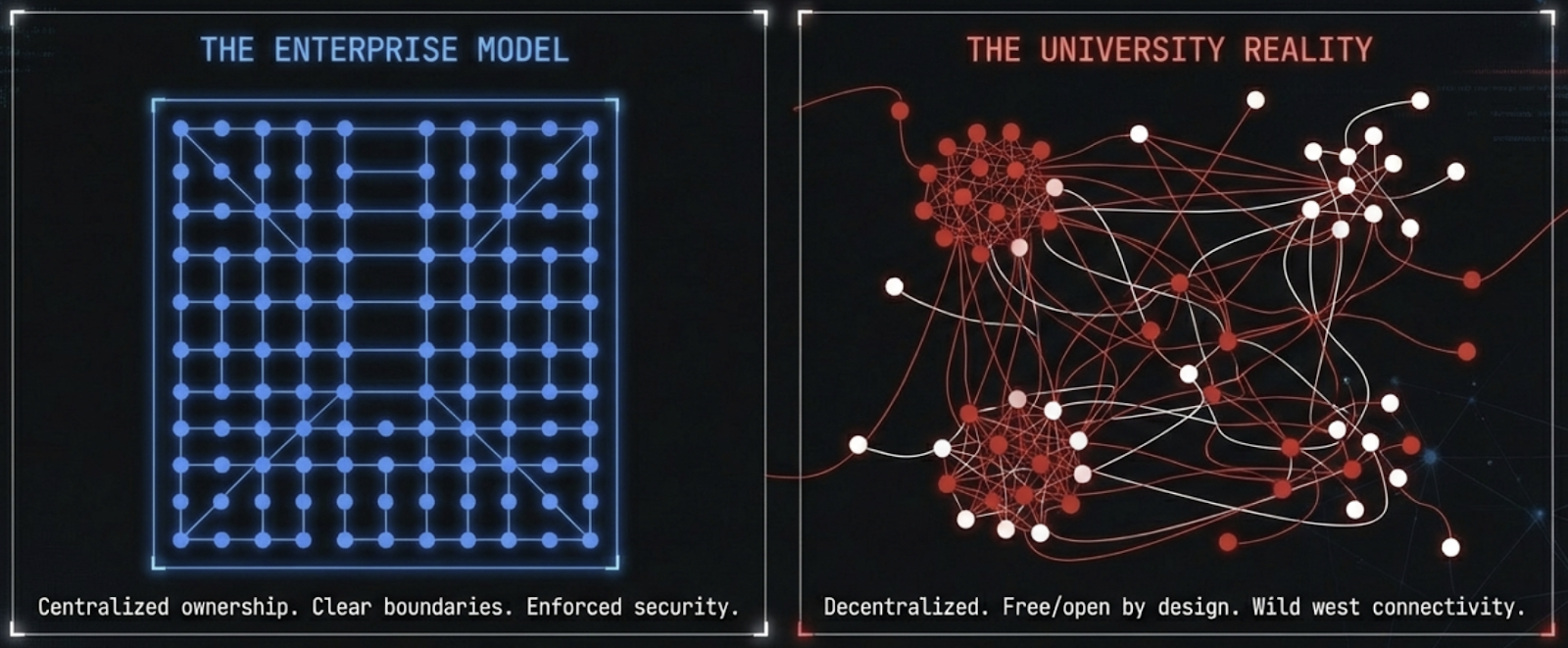
Universities Are Not Enterprises
Universities do not operate like corporations and penetration testing needs to reflect that reality.
Enterprise environments are centralized, ownership is clear, and security boundaries are enforced. Universities are the opposite by design, they’re free and open.
Departments run their own systems. Research labs experiment freely. Faculty deploy tools for teaching and research. Students are encouraged to build real applications. All of this often happens on shared networks and shared infrastructure. In many cases, this architecture has existed for years because it “hasn’t caused a problem.”
Public-facing systems are everywhere. Course pages, research project sites, student portfolios, departmental websites, and experimental web applications are routinely exposed to the internet. Many of these are built by people who are not security professionals, and they should not be expected to be. The problem is not that these systems exist. The problem is where they exist and what could access them.
What makes universities innovative also makes them fragile. When penetration tests rely on enterprise assumptions, they often miss highly vulnerable systems.
The Overlooked Attack Surface: Student and Faculty Web Hosting
Student and faculty web hosting environments are one of the most consistently overlooked risks in higher education penetration testing.
These environments often include custom authentication, file uploads, server-side scripts, database connections, and legacy frameworks. They are built for learning, teaching, and experimentation. Security is rarely the goal.
These environments are an OWASP Top 10 playground. Vulnerabilities like remote code execution, command injection, insecure file uploads, and authentication bypass are the norm.
The risk isn't the typical academic theory. These systems are:
Public
Routinely scanned by attackers
Easy to exploit
Often connected to shared infrastructure
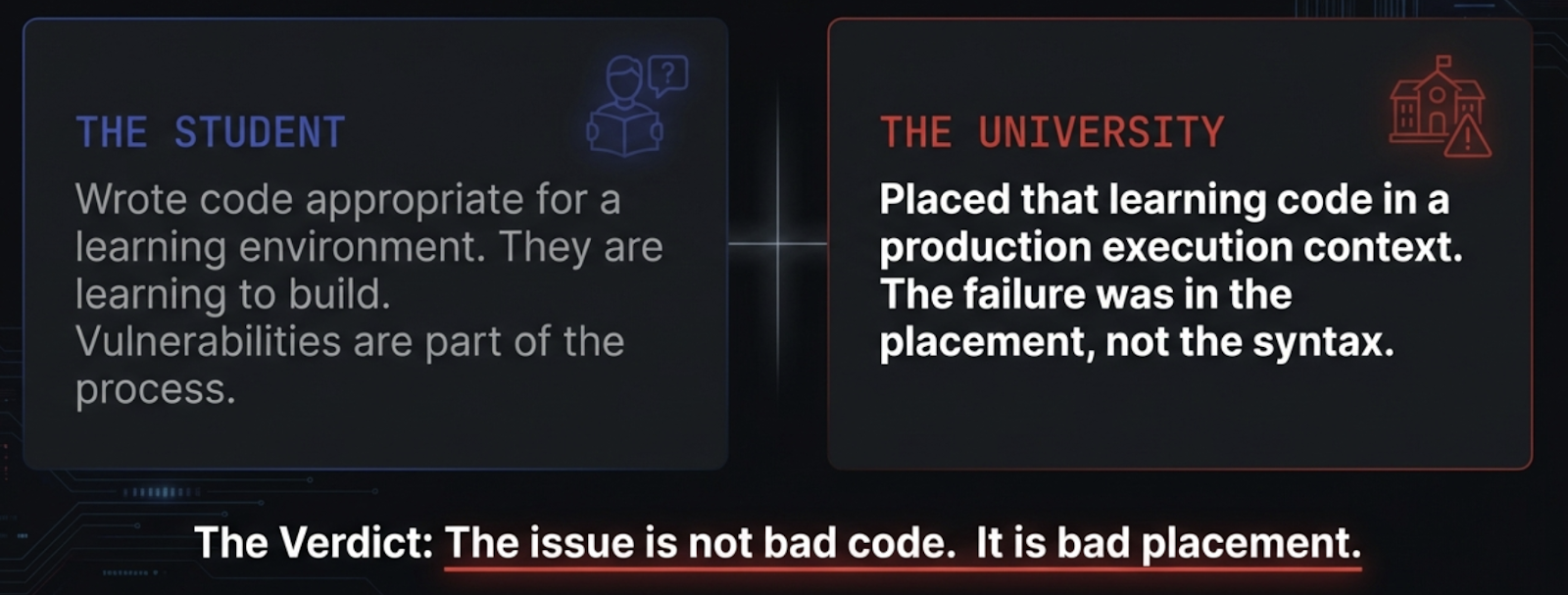
Case Study: When a Student Web App Compromised the Root Domain
During a recent penetration test, we discovered a university hosted both student and professor web applications on the same primary web server as the university’s root domain.
Each student or faculty project lived in a directory under the main web application. Different pages. Different owners. Same execution environment. Same permissions.
From an organizational standpoint, this felt efficient. From a security standpoint, it was catastrophic.
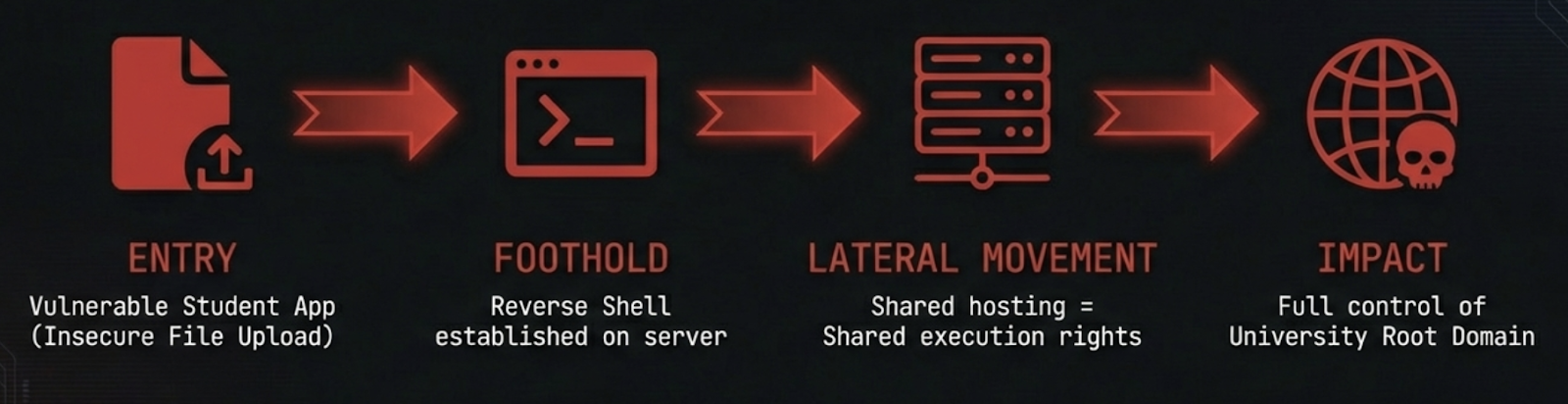
What We Found
Multiple student and faculty applications were vulnerable to remote code execution.
In practice, they functioned as reverse shell playgrounds.
We identified:
Insecure file upload handlers
Command injection in administrative scripts
SQL injection paths that escalated to OS-level execution
Reverse shells were trivial to obtain. Once we had execution through one application, we had execution on the server itself.
There was no isolation between student code and production systems.
Impact
Once execution was achieved through a single student application, the impact was immediate and severe:
Full control over the root domain web application
Ability to deface the university’s primary website
Ability to disrupt services
This was not a student failure, but an architectural one.
The student wrote code appropriate for a learning environment. The university placed that code in a production execution context.
Why This Happens So Often in Higher Education
This pattern is common because the incentives are baked into higher education. Students are learning. Professors are experimenting. Security is not the goal of these systems, and it should not have to be.
Shared hosting feels convenient. Legacy decisions persist. Over time, dozens or hundreds of applications accumulate in an environment never designed to handle them safely.
Universities need environments where learning and experimentation can happen without putting institutional systems at risk.
What Should Change: Penetration Testing Scope and Architecture
Penetration Testing Scope for Universities
If a system is:
Internet-facing
Hosted on university infrastructure
Running custom code
It must be in scope. Attackers do not care whether an application is “just a student project.” Scope exclusions do not stop exploitation.
University penetration testing should explicitly include:
Student project hosting
Faculty and research websites
Departmental web applications
Any public-facing custom code
The goal is not to shame student developers. It is to identify architectural risk.
Secure Architecture Guidance: The Non-Negotiable Principle of Isolation
This is the non-negotiable part: Student and faculty code must not run in shared execution environments with production systems.
That means:
No shared CGI bins
No shared interpreters
No shared file system access
No student code running with elevated privileges
Isolation is the control that matters.
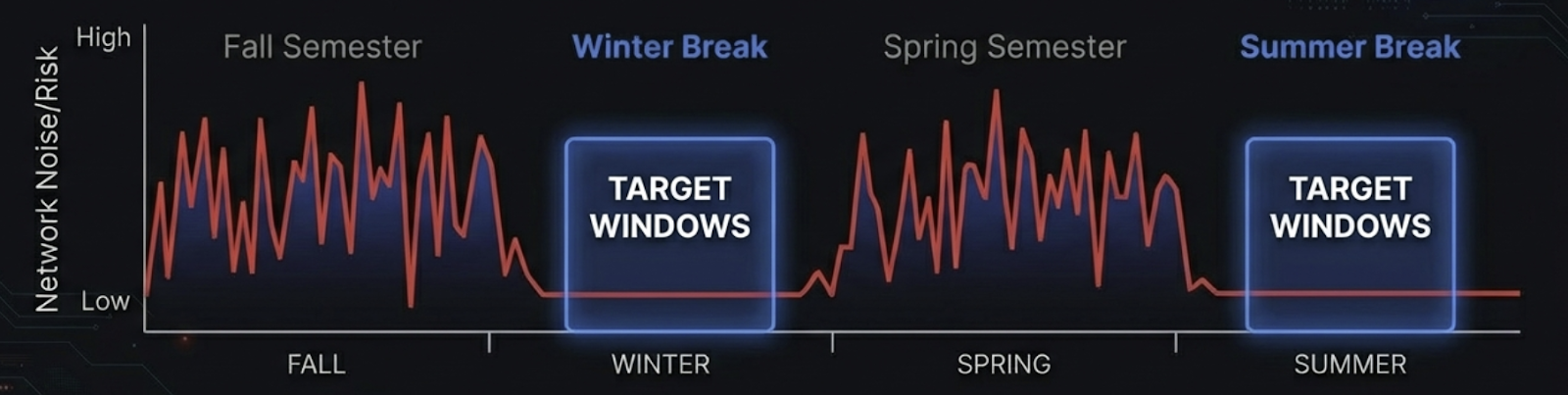
Timing Matters: Schedule Penetration Testing Around the Academic Calendar
Universities are noisy environments during active semesters.
Thousands of student devices, transient systems, and out-of-scope assets complicate testing and increase risk. Outages during class time have a real impact.
Testing during academic breaks:
Reduces background noise
Simplifies scoping
Lowers operational risk
Improves test accuracy
Penetration testing is inherently disruptive. Scheduling it intelligently is part of risk management, not an afterthought.
What “Good” Looks Like
Good security in higher education does not mean locking everything down.
It means:
Treating student environments as untrusted by default
Isolating experimentation from institutional systems
Writing penetration test scopes that reflect reality
Aligning testing with academic operations
This is how universities enable innovation without absorbing unnecessary risk.
Closing Thoughts
Universities do not need to be secured like corporations.
But they do need to recognize when experimentation becomes institutional risk.
Students should be able to build vulnerable applications. Faculty should be able to experiment freely. Those activities just cannot live in places where a single flaw compromises the entire institution.
University penetration testing that acknowledges this reality is the difference between checking boxes and insightful security excellence.