We hunt for leaks in the developer ecosystem outside of your perimeter.
WELCOME TO EXPLOIT SHIELD
Exploit Shield hunts for publicly exposed credentials, tokens, and other first- and third-party leaks on clear web developer ecosystems to reduce your attack surface before compromise.

Where We Monitor
Exploit Shield continuously monitors high-risk public developer ecosystems
GitHub
Public repositories and commit history are continuously scanned for exposed secrets, hardcoded credentials, infrastructure configuration files, OAuth keys, and internal documentation.
Postman
Public workspaces, collections, and environments are analyzed for API keys, bearer tokens, authentication headers, environment variables, and internal system references that could expose production services.
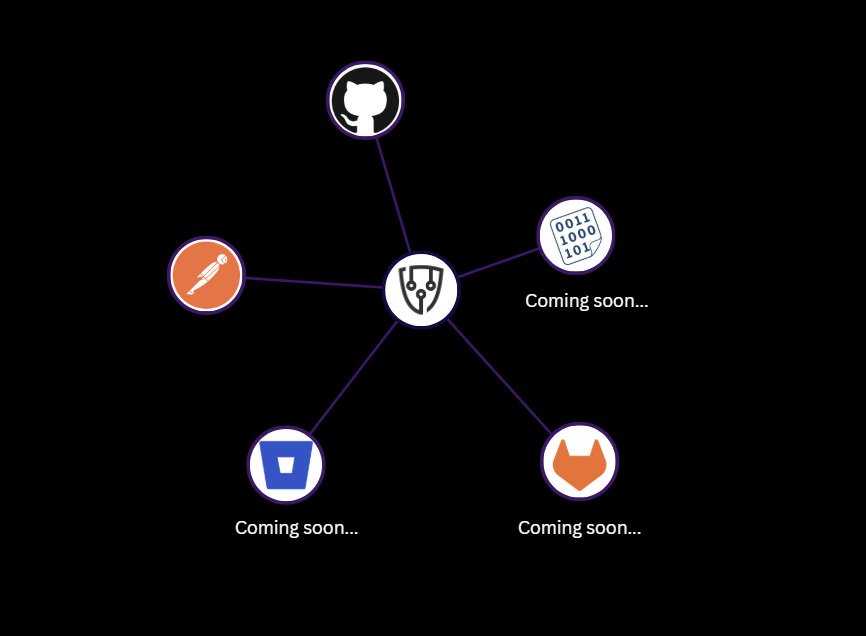
How It Works
The process it simple: Tell us about yourself, then watch the leaks populate.
Onboard
We align on the signal we should hunt for and the partners that expand your exposure surface.
- Keywords: product names, internal systems, unique identifiers
- Domains: your primary domains and known subdomains
- Third-party vendors: vendor domains that touch your environment
Quality beats quantity here. Tight inputs drive cleaner findings and fewer false positives.
Discover
ExploitShield continuously searches public sources and reduces raw results into high-signal candidates.
- Proprietary search: finds relevant repos, artifacts, collections, and snippets
- Enrichment: adds context around where it lives and what it contains
- Refining + filtering: deduplicates, scores, and removes obvious noise
What remains is a shortlist that is worth triaging.
Triage
We determine what it is, who it impacts, and how bad it is, so response and remediation can begin.
- Impact: what was exposed and why it matters
- Scope of impact: affected systems, accounts, vendors, or business units
- Blast radius: how your organization is affected and what could be abused
The output is an actionable finding you can assign, investigate, and remediate.
Actionable Threat Intelligence
FINDINGS INCLUDE A SUMMARY OF THE LEAK, INVENTORY OF ARTIFACTS, LEAK ATTRIBUTION

Case Studies
HOW EXPLOIT SHIELD ENABLED TEAMS TO PREVENT MASSIVE BREACHES
Gateway to Mass Exposure
A single public personal GitHub repository contained production configuration files for 23 credit unions and banks. Exposed artifacts included:
- Core banking URLs (Symitar, Fiserv DNA)
- Visa and Mastercard integration credentials
- Institution-specific production secrets
The repository was public from May 2022 to February 2025. None of the affected parties detected it until Exploit Shield was engaged.
Enterprise API Ecosystem Exposure
An employee moved private Postman collections to a personal account and made them public. Exposed artifacts included:
- Hundreds of API credentials
- Production and non-production secrets
- Authentication tokens actively in use
The exposure persisted for over a year before disclosure. The organization was unaware until Exploit Shield was engaged.
The 20-Year Admin Repository
While using Exploit Shield for OSINT recon for a penetration test, we discovered a public personal GitHub repository containing:
- 20 years of internal sysadmin notes
- Plaintext domain administrator credentials
- Service account passwords
The repository was not malicious. It was a trusted employee preserving personal notes before leaving the company.
Where Exploit Shield Sits
EDR sees endpoints.
Pentesting sees authorized systems.
ASM sees perimeter infrastructure.
Exploit Shield hunts leaks on public developer platforms.
When secrets leak outside your environment, we detect them, structure the evidence, and feed it into your existing workflows.

Built to Feed the Systems You Already Use
Integrations
Exploit Shield is not another dashboard your team has to monitor. Findings are structured and delivered directly into the systems your security and IT teams already operate.
Jira
OpenCTI (STIX 2.1 compatible)
Splunk

Additional SIEM, TIP, and workflow integrations are available upon request. Exploit Shield is API-driven and designed to integrate into mature security environments.
AI Use Statement
Our solution uses AI as a supplemental capability to efficiently identify and attribute publicly exposed sensitive data, while maintaining human analyst oversight to ensure accuracy and reduce false positives.
Built on a locally hosted, pretrained open-source model, the AI is not trained on customer data and operates by correlating keywords to support attribution. The system is highly customizable, privacy-focused, and designed with a human-in-the-loop approach to mitigate bias and ensure responsible use, as it does not generate new content or make autonomous decisions.
We do not ingest or store customer data, environments are isolated by client, and data is encrypted in transit with secure authentication controls. Overall, AI is intentionally limited in scope and used to accelerate analysis, reduce manual effort, and support faster, more reliable identification of potential data exposures.