Penetration Testing Services
VIDEO - HOW TO SCOPE A PENTEST
Assumed Breach Pentest
Often referred to as Red Team Lite.
An assumed breach engagement simulates a scenario where an attacker has already gained an initial foothold inside your network. We test lateral movement, privilege escalation, and access to sensitive systems to measure how far an adversary could realistically go. The objective is to expose internal weaknesses and validate detection and response capabilities.
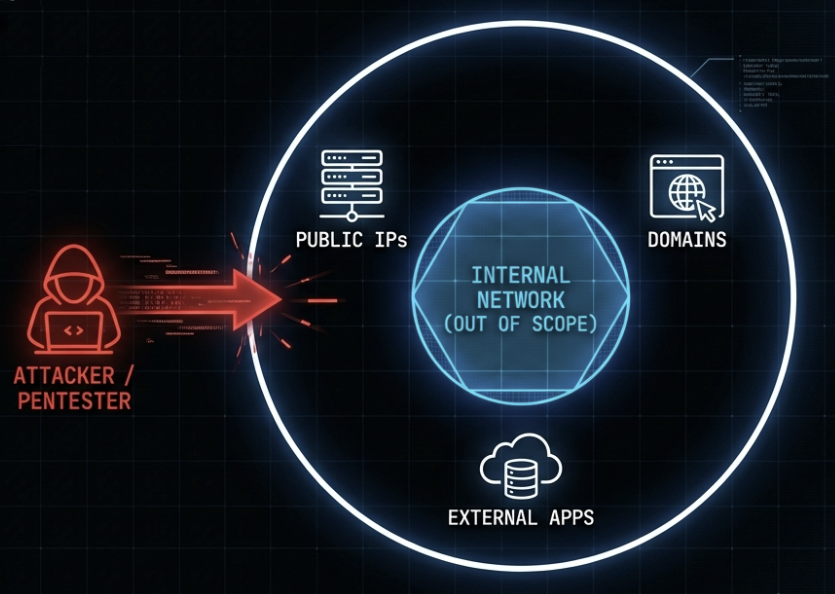
External Network Pentest
An external penetration test is a simulated attack by cybersecurity experts on an organization's internet-facing systems, like websites and email servers, to identify exploitable vulnerabilities.
Internal Network Pentest
An internal network penetration test, or assumed breach, simulates cyberattacks within an organization's internal network to identify vulnerabilities in systems, devices, and configurations, enhancing internal security and resilience.
Web/Mobile Application Security Assessment
A web or mobile application penetration test assesses the cybersecurity of web and mobile applications, identifying and mitigating vulnerabilities to protect against data breaches and unauthorized access.
API Pentest
An API penetration test assesses the cybersecurity of application programming interfaces, identifying vulnerabilities in authentication, data handling, and access controls to ensure secure communication between systems and protection against unauthorized access or data breaches.
Physical Pentest
A physical penetration test simulates unauthorized physical access attempts to test and improve the effectiveness of an organization's physical security measures and controls.